Internet safety best practices Change password regularly

By statistics, each person has approximately three passwords in use for cyber activities. Most of these passwords are over 5 years old and were used in multiple places and could be known by third-party as well (relatives, friends, classmates, etc). This happens because sometimes people share their password with other people to allow access to their personal data online for different reasons. Time passes and passwords do not get changed.
However, the deeper problem is that the password has to be changed because nowadays a lot of hacks appear and information about a person can be found in leaked databases with passwords in clear form.
Some cyber-criminal groups work in this field by using leaked credentials to access personal data of potential victims using information from previous passwords used. This type of attack is known as – password reuse attack.
How deep is your complex password?!
Lot of us using complex passwords that could be easy to the predicate, such as P@$$W0RD, Password123, …etc.
But actually, the strong password is depending on its length, the more characters you are using the better quality of password you have.
Nowadays the concept of the password is getting vanishing cause a lot of manufactures to tend to move with password-less authentication using fingerprints or facial resonation instead.
Hackers move forward and reach out looking for new techniques to crack these newly authentication systems to bypass and own the systems.
Don’t share SMS Message info (one-time password).
SMS messages nowadays used on the internet for authorization and authentication. People should understand that the last thing you should share with someone is the SMS message you get on your phone. Why? Because having this information attacker can easily recover access for your email, access your bank account or iCloud, which can be a really big problem.
All big corporations use SMS for two-factor authentication and it saves employees in cases someone was able to access his or her passwords.
Scammers use different techniques to get your SMS. Mostly they give you a call asking to provide SMS code because of some security reasons and verifications. The problem is that most people do not pay attention to the content of SMS and the reason for this request and give away this information which allows the attacker to be easily manipulated and completely exposed to the cyber-criminal.
Don’t click blindly
A big amount of modern cyber-attacks nowadays come from your email box. It is extremely important to understand that 20-30% of the spam you receive is most likely a phishing email sent to a large number of people, however, sometimes they get inbox and in this case, people do not pay attention to URLs they click on the text of the email and actions asked to perform.
Cybercriminals regularly target their victims, but sometimes it can be a personalized spear-phishing attack which can cause big problems because the person may not even realize it was a phishing attack.
One of the most important things on how to avoid this situation is to follow simple steps during the reading of emails: understand the purpose of
email, check on texts and details of the email, check for suspicions you may have, look on the sender, and if everything good – double-check URL you clicked in order to check is URL you came for is legit.
Check download files
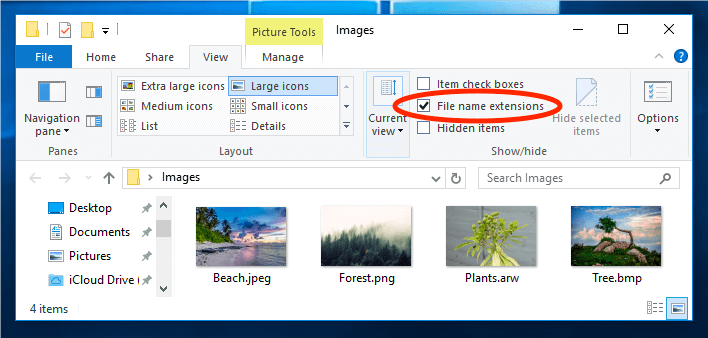
During file download, it is important to know which extensions are safe to run and which one can cause problems. Let’s talk about this deeper:
Exe, MSI, bat, SCR (screensaver), VBS, hta, js, reg, key, and file extensions you better be sure to know what you are running.
Modern browsers ask and notify their user about potentially dangerous file downloads. Sometimes you use torrents to download files to download clients which may not notify you about the danger you are facing.
Try to pay attention to files you are opening because in a blink of an eye all your data can be sent to a third-party server or attacker who can additionally get control over your PC.
Try to keep your icons big and see extensions in order to avoid spoofing.
If the file is malicious try to check it on the virustotal.com website.
Encrypt your precious information
Saving confidential information on computer systems is a crucial task should be treated differently from saving any other documents, based on the business impact analysis to identify the damages if this confidential information theft, stolen, exposed on public, or even deleted permanently on purpose by adversaries.
Encrypting this information with proper safeguards and countermeasures could mitigate the identified risks and provide certain assurance levels to protect and maintain.
System updates
Attacks on users can include not only social engineering and data leak attacks, but also exploitation of outdated software.
This type of attack includes usage of exploits which can be run against outdated software like:
The operating system, PDF reader, Microsoft Office, Browser, and other software used on a daily bases.
The update should not be avoided or canceled, especially the critical ones.
Try to update OS, Software, and antivirus signatures on your antivirus, it can save you from further problems with malware on your device.
By Yasser Sallam
InfoSec consultant
Cairo, Egypt